During youth, and well into adult hood, we are constantly reminded to protect ourselves from the viruses that plague our world. Starting with the wise warnings from mom, reminding us to wash our hands and brush our teeth, to our girlfriends threat of “no glove, no love”.
We as humans, have a natural tendency to protect ourselves from harmful elements. If you have ever had a cold, then you have undeniable proof that it is possible to contract a disease from viruses, but what about your Android phone? With the varying information on whether or not the OS is capable of contracting a virus, it is difficult to know how to protect ourselves, or even if we need protection.
In November 2011, Google’s Open Source Programs Manager assured us that the Android OS would not be the target for the next Independence Day. During his lengthy G+ post about Open Source logistics, he stated:
Yes, a virus of the traditional kind is possible, but not probable. The barriers to spreading such a program from phone to phone are large and difficult enough to traverse when you have legitimate access to the phone…
From his mouth to your ears, It IS possible to contract a virus on the Android Operating System. Since his post last year, Google’s “barriers” that help prevent malicious attacks have been compromised. At the Summercon conference last Monday, Mobile security researchers Jon Oberheide and Charlie Miller explained how easily someone could circumvent Bouncer, the Android malware scanner.
In its last quarter, McAfee reported a huge increase in mobile malware, which they attributed to being “almost solely at the Android platform”. They reported that “Android threats now reach almost 7,000, with more than 8,000 total mobile malware in our database.”
With this information, it could be safe to say that yes, we need to protect our phones from the scrupulous people who wish to hack our devices, and steal our personal information, but how do we do that? The first solution to any problem is to become aware of the eminent dangers, and, to do that, you must know what threats are out there.
DDSpy
Recently released in the wild, DDSpy secretly attaches itself to your device as a fake Gmail app which is designed to steal your personal information.
Because DDSpy is installed into the Android device without your knowledge, you won’t see any signs that you’ve been bugged. However, every call you make and every SMS message you send will be recorded in the database to be uploaded in the configured email. (NQ Mobile)
Android.Opfake
This sneaky malware uses premium-rate SMS messages to trick unsuspecting Google Play customers into paying for apps that would otherwise be free.
There are several variants of Android.Opfake hosted on these sites with different methods to lure victims there initially, and different steps involved in each scam. (Symantec)
Android/Adboo.A
For those of you in who like to send mms greeting cards, you may want to think twice. This Trojan targets Chinese users by allowing them to choose standard greeting card templates, than requests you to enter contact info. Once you choose to submit the card, instead of submitting it to your chosen contact, it gives you an error message.
We noticed that the app did do something else though. On selecting the Contacts options, it silently obtained the following information from the device:
1) Phone Model
2) Android Version
3) Phone number
4) International Mobile Equipment Identity (IMEI) number (f-secure)
The above cases only represent 3 out of 3063 threats that are currently accounted for in F-Secures Mobile Threat Report, Q12012. With so many threads in the wild, what can you do to best protect yourself?
- Android warns you what permissions an application wants to access for a reason. Do not be quick to click by agreeing to the permissions before reviewing them. Cross reference the privacy policy with the permissions being requested.
- Resist the temptation to download applications outside of Google Play and other reputable sources. Your safest bet is to not download applications from unknown sources.
- Research the app before downloading it; Check the comments, ratings and developer profiles. Keep an eye on the behavior of your phone. If it is acting up, it could be a sign of malware or other threats.
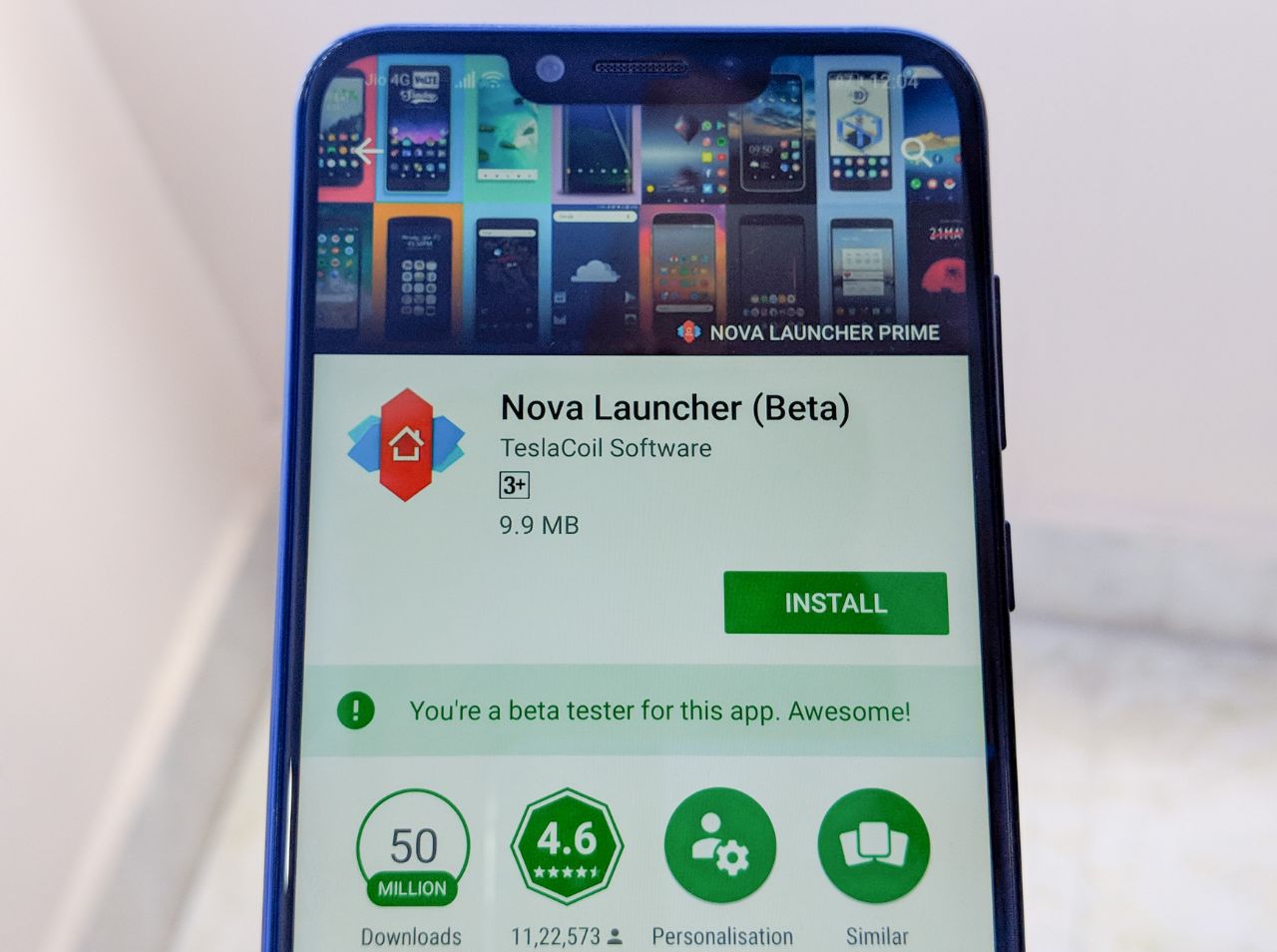
- Download Android mobile security apps. There are many free, as well as paid apps in the market.